Protocols/MSNP/Scenarios/Mac
| MSNP Protocol |
| Introduction • Terms • Clients |
| Reference |
| Error List • Commands • Relying Party Suite • Spotlife |
| Services |
| XMPP • HTTP Gateway • Tabs • Activities |
| Documentation |
| Development Tools • MSNP Grid |
| Polygamy • URLs used by MSN |
| Documents |
| Protocol Versions |
| Version 21 |
| Version 18 |
| Version 16 |
| Version 15 |
| Version 14 |
| Version 13 |
| Version 12 |
| Version 11 |
| Version 9 |
| Version 8 |
| Version 2 |
| MSNC |
| Introduction • P2P • Object Descriptor • Display Pictures • File Transfer |
| Scenarios |
| Microsoft Messenger for Mac |
| MSNP on WebTV (MSNTV) |
Messenger:mac is a client made by Microsoft that implements MSNP, available on Mac OS. It was only 32-bit, making it incompatible with recent versions of macOS.
Protocol
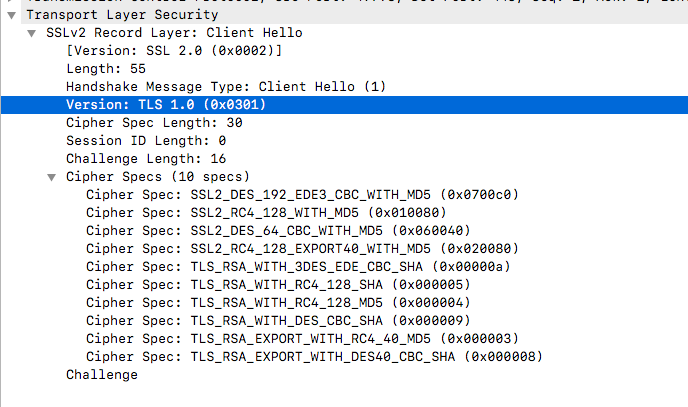
From our testing, all the versions we have tested (6.0.3, 7.0.2, 8.0.1) use TLSv1 to connect to the login servers, HOWEVER it just uses an old record layer. More information about this would be very appreciated.
- 6.x, 7.x: MSNP14, MSNP13
- 8.x (including beta): MSNP16, MSNP15, MSNP14, MSNP13
This is the only official Microsoft client that uses the TWN auth method after MSNP15 (SSO/RPS was introduced in MSNP15).
Logging
You can enable connection logging on M:M 7 and 8 by enabling it in Preferences (Cmd+,). The file location will be ~/Documents/Microsoft Messenger.log on M:M 7 and ~/Library/Logs/Microsoft Messenger.log on M:M 8.
Changing servers
To change the servers, you'll have to edit the binary data itself using an hex editor.
There's a configuration file (plist) located in ~/Library/Preferences/Microsoft/com.microsoft.Messenger.plist(6.x, 7.x) and ~/Library/Preferences/com.microsoft.Messenger.plist(8.x) that caches some server values (ABCH Server, NS Server, Gateway Server) that should also be changed if the app has been opened before.
CVR commands sent
M:M 8.0.1
CVR 2 0x0409 mac 10.13.6 i386 macmsgs 8.0.1 macmsgs me@andreadoria.cf
M:M 8.0.0 beta
CVR 2 0x0409 mac 10.13.6 i386 macmsgsbeta 8.0.0 macmsgsbeta me@andreadoria.cf
M:M 7.0.2
CVR 2 0x0409 mac 10.9.6 i386 macmsgs 7.0.2 macmsgs me@andreadoria.cf
M:M 6.0.3
CVR 2 0x0409 mac 10.9.6 i386 macmsgs 6.0.3 macmsgs me@andreadoria.cf
All of these requests were sent using macOS 10.13.6, but 6.x and 7.x seem to send the client operating system version as 10.9 (probably a cap?)
Odd quirks
Messenger:mac only reads the PassportURLs Header from the Passport Nexus if it ends with ConfigVersion=14.
It uses TWN even on MSNP16, so it gets the ABCH token from the DALogin value from the PassportURLs header. It's currently unknown how it gets the token itself, more information would be appreciated.